By Catalin Cimpanu
In an emergency out-of-band update released late last night, Microsoft fixed a vulnerability in the Microsoft Malware Protection Engine discovered by two Google security experts over the weekend, and which the two described as “crazy bad” and “the worst Windows remote code exec in recent memory.”
While initially the two Google experts didn’t reveal what Windows feature the bug was found in, the veil of mystery lifted yesterday when both Microsoft and the two experts shared more details about the issue.
Vulnerability affects Microsoft Malware Protection Engine
As per the two sources, the bug affects the Microsoft Malware Protection Engine (MsMpEng), a core service that ships with Windows 7, Windows 8.1, Windows 10, and Windows Server 2016, and which is the core of many of Microsoft security tools, such as:
- Windows Defender
- Microsoft Security Essentials
- Microsoft Endpoint Protection
- Microsoft System Center Endpoint Protection
- Windows Intune Endpoint Protection
- Microsoft Forefront Security for SharePoint Service Pack 3
- Microsoft Forefront Endpoint Protection 2010
According to the Google experts, the bug is a “type confusion” vulnerability in NScript, the MsMpEng component that handles “any filesystem or network activity that looks like JavaScript.”
Vulnerability is trivially exploitable
The researchers say the issue can be exploited with no user interaction needed.
This includes scenarios such as sending an email with the exploit included in the message’s body, hosting malicious JavaScript code inside a web page, or by delivering a JS exploit to thousands or millions on users, via ads on reputable sites.
“Vulnerabilities in MsMpEng are among the most severe possible in Windows, due to the privilege, accessibility, and ubiquity of the service,” Tavis Ormandy, one of the Google researchers says.
This is because the service runs without sandboxing — a basic and very efficient security feature —, but also because the service runs as
NT AUTHORITY\SYSTEM, a system-level user with no limitations.
Furthermore, the service is included by default on all recent Windows operating system, exposing hundreds of millions of PCs to remote hacking.
Microsoft patches issue within days
Unlike past incidents, where Microsoft has allowed exploited zero-day vulnerabilities to fester in the wild without being bothered to deliver a patch for months, this time around, the company moved lightning fast to address the issue.
In just a few days, the company had prepared and already shipped a patch to fix the vulnerable MsMpEng service.
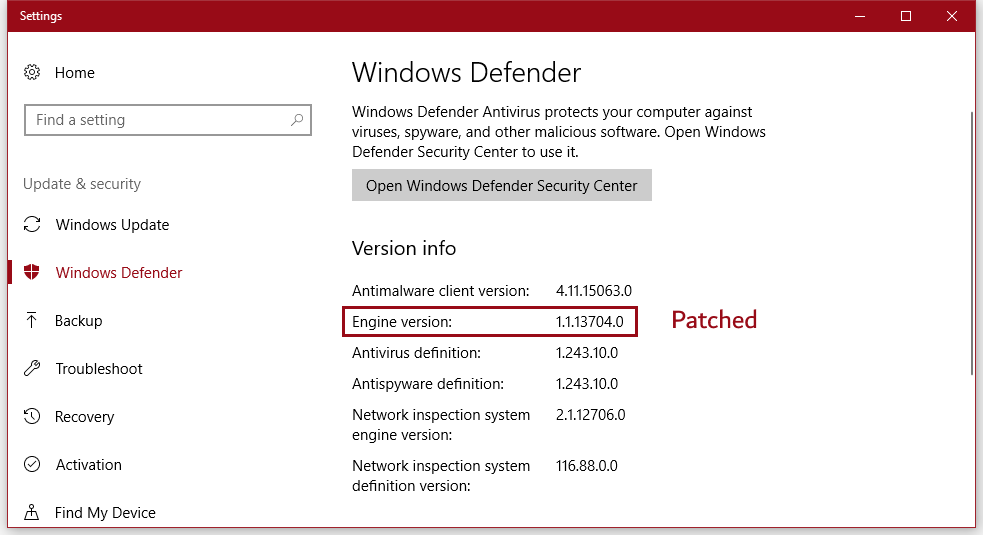
According to a Microsoft advisory, the first version of the Microsoft Malware Protection Engine affected by this flaw is v1.1.13701.0. The issue has been patched in v1.1.13704.0, released a few hours ago, and which has already reached some users (screenshot above).
Microsoft also said that on latest Windows platforms, the risk of exploitation should be lower if the user has turned on Windows CFG (Control Flow Guard), a security feature that can make exploitation of memory-based vulnerabilities much harder.
The vulnerability is tracked as CVE-2017-0290. The two Google researchers also released proof-of-concept exploit code. The entire exploit fits in a tweet. To help spread the word about this issue, US-CERT has also released an accompanying alert.













Leave A Comment
You must be logged in to post a comment.