Hiring a professional developer is a wise investment if you’re serious about creating a successful WordPress website.
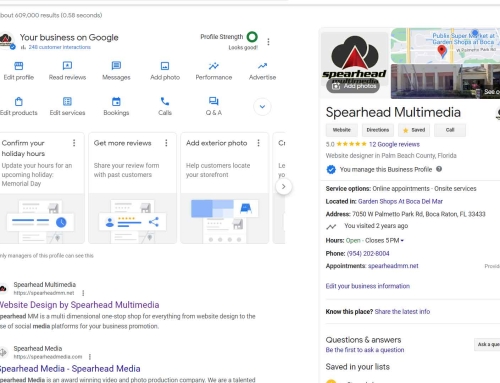
There are many reasons to use a professional WordPress developer, such as Spearhead Multimedia, to build or maintain your website. Here are a few of the most important:
- Expertise: WordPress developers have the skills and experience to build a functional and visually appealing website. They are familiar with the latest WordPress features and best practices and can help you create a website that meets your specific needs.
- Time savings: Building a website from scratch can be time-consuming and complex, even if you use WordPress. Hiring a professional developer can save you significant time, allowing you to focus on other aspects of your business.
- Peace of mind: Knowing that your website is in the hands of a professional can give you peace of mind. WordPress developers can help you keep your website secure and up-to-date, and they can troubleshoot any problems that may arise.
- Scalability: WordPress is a scalable platform, meaning that it can be easily adapted to meet the changing needs of your business. A professional developer can help you build a future-proof website that can grow with your business.
- Cost-effectiveness: Hiring a professional WordPress developer may seem like a significant expense upfront, but it can save you money in the long run. A professional developer can help you save time and money in the long run by avoiding costly mistakes and ensuring that your website is properly maintained.
We highly recommend hiring a professional developer if you are considering building or maintaining a WordPress website. The benefits of hiring a professional far outweigh the costs, and it can help you create a successful and hassle-free website.
Here are some additional benefits of hiring a professional WordPress developer:
- We will host your websites on Spearhead Multimedia’s high-performance servers.
- We will help you purchase and manage your domain names.
- We will install and configure only the highest-rated WordPress plugins and themes.
- We will help you create custom content and a unique design for your website.
- We will provide ongoing support and maintenance for your website.
- We will help you with bulk emailing, website promotion and marketing, SEO, and PPC.
If you are serious about creating a successful WordPress website, I encourage you to hire a professional developer, such as Spearhead Multimedia. We can help you take your website to the next level and provide a fast and consistent return on your investment.
Expertise and Experience: A professional WordPress developer, such as Spearhead Multimedia, has the knowledge and experience to create a high-quality website optimized for search engines and user experience.
Spearhead Multimedia’s WordPress developers deeply understand the platform, its features, and its potential. We can help you choose the right plugins, themes, and settings for your needs and can troubleshoot any problems that may arise.
With Spearhead Multimedia, you can customize your website to your specific needs and requirements. We can create custom themes, plugins, and functionalities tailored to your business needs.
Related: 25 Reasons Your Business Should Switch to WordPress
Spearhead Multimedia can create a custom design for your website that reflects your brand and your unique needs. They can also help you add unavailable features and functionality not found in off-the-shelf themes.
Spearhead Multimedia can complete the project on time, which is especially important if you are working on a tight deadline. We have the expertise to create and launch a website quickly and efficiently.
Building and maintaining a WordPress website can be time-consuming, especially if you don’t have the skills or experience. Spearhead Multimedia can take care of all of the technical details so you can focus on other aspects of your business.
When you hire Spearhead Multimedia, you receive ongoing technical support. If you encounter any issues with your website, we troubleshoot and fix the problem quickly.
Knowing that your website is in the hands of a qualified professional can give you peace of mind. You can be confident that your site is secure, up-to-date, and optimized for search engines.
Related: The Unstoppable Power of WordPress
Spearhead Multimedia stays updated with the latest trends and technologies in website development. Your website will be created using the latest best practices and standards.
Although hiring a professional developer may seem expensive, it can be cost-effective in the long run. A high-quality website will increase your business’s revenue and improve your online presence, leading to more customers and higher profits.
As your business grows, your website will need to grow with it. Spearhead Multimedia website designs and servers are scalable to handle increased traffic and demand.
Hiring a professional WordPress developer can save you time, provide technical support, create a unique design for your website, and help your business grow.
















Leave A Comment
You must be logged in to post a comment.